National security agencies face unprecedented data challenges. From classified intelligence reports to real-time surveillance feeds, these organizations must store, access, and protect massive volumes of sensitive information while maintaining operational readiness around the clock. Storage Area Network (SAN) technology has emerged as the foundational infrastructure solution that enables defense and security agencies to meet these critical requirements.
SAN storage provides the high-performance, secure, and scalable foundation necessary for national security operations. Unlike traditional direct-attached storage systems, SAN architectures create dedicated networks that connect multiple servers to centralized storage resources, delivering the reliability and performance that mission-critical applications demand. This centralized approach enables security agencies to consolidate their storage infrastructure while maintaining the stringent security controls and availability requirements that national defense operations require.
The complexity of modern security threats and the exponential growth of intelligence data have made robust storage infrastructure more critical than ever. SAN storage technology addresses these challenges by providing enterprise-grade features specifically designed for high-security environments where data integrity, availability, and confidentiality are non-negotiable requirements.
Benefits of SAN in National Security Applications
Enhanced Security Architecture
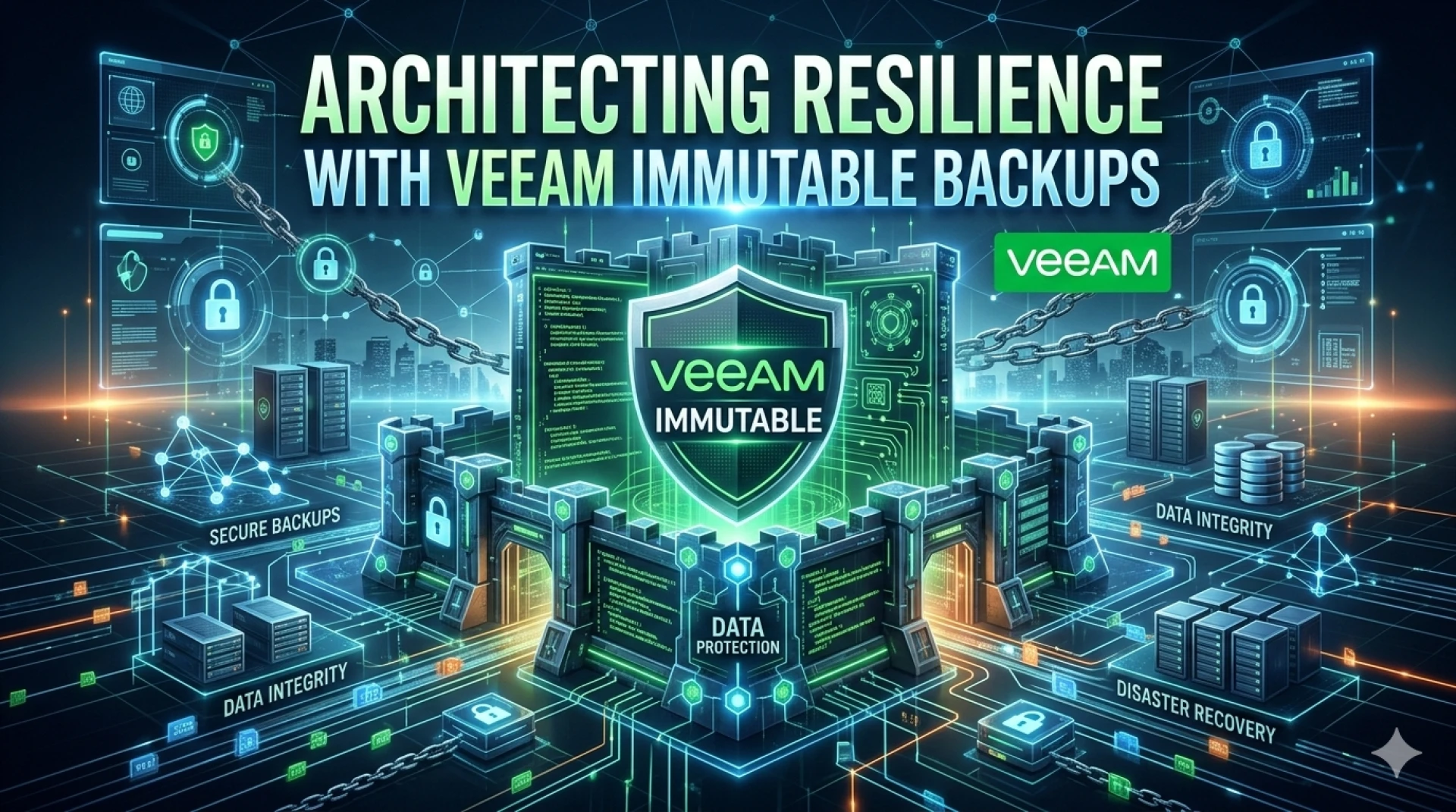
SAN storage systems offer multiple layers of security controls that align with federal security frameworks. The isolated network architecture inherent in SAN deployments creates a dedicated data pathway that can be secured independently from general network traffic. This isolation reduces attack vectors and provides administrators with granular control over data access patterns.
Advanced encryption capabilities protect data both at rest and in transit across the SAN fabric. Hardware-based encryption engines deliver high-performance data protection without impacting application performance, ensuring that classified information remains secure throughout its lifecycle.
High Availability and Fault Tolerance
National security operations cannot tolerate storage downtime. SAN architectures provide redundancy at every level, from dual-controller storage arrays to multipath connectivity options. Automatic failover mechanisms ensure continuous data availability even during hardware failures or maintenance activities.
Clustering capabilities enable active-active configurations where multiple storage controllers share workloads and provide seamless failover protection. This distributed approach eliminates single points of failure and ensures that critical intelligence systems remain operational during component failures.
Scalability for Growing Data Requirements
Defense agencies generate terabytes of new data daily through surveillance systems, intelligence gathering, and operational activities. SAN storage scales both vertically and horizontally to accommodate this growth without disrupting existing operations.
Scale-out architectures allow organizations to add storage capacity and performance by incorporating additional nodes into the SAN fabric. This modular approach enables agencies to align infrastructure investments with operational requirements while maintaining consistent performance characteristics across the entire storage pool.
Centralized Management and Resource Optimization
SAN storage consolidates disparate storage resources under unified management platforms. This centralization reduces administrative overhead while improving resource utilization across multiple applications and departments.
Quality of Service (QoS) controls ensure that mission-critical applications receive priority access to storage resources. Administrators can define service levels for different data types and applications, guaranteeing performance for time-sensitive intelligence operations while efficiently utilizing available capacity.
Critical Use Cases for SAN Storage in Defense Operations
Secure Data Storage for Classified Information
Classified data storage requires strict adherence to federal security standards including FIPS 140-2 validation and Common Criteria certifications. SAN storage platforms provide the security controls necessary to meet these requirements while delivering the performance needed for large-scale classified data repositories.
Multi-level security implementations enable agencies to store data at different classification levels within the same infrastructure while maintaining strict separation controls. This capability reduces infrastructure complexity while ensuring compliance with information handling requirements.
Surveillance and Intelligence Data Management
Modern surveillance systems generate continuous streams of high-resolution video, sensor data, and metadata that require immediate storage and rapid retrieval capabilities. SAN storage handles these demanding workloads through high-bandwidth connectivity and parallel processing capabilities.
Tiered storage strategies automatically move aging surveillance data to cost-effective storage tiers while maintaining rapid access to recent information. This approach optimizes storage costs while ensuring that analysts can access historical data when needed for pattern analysis and threat assessment.
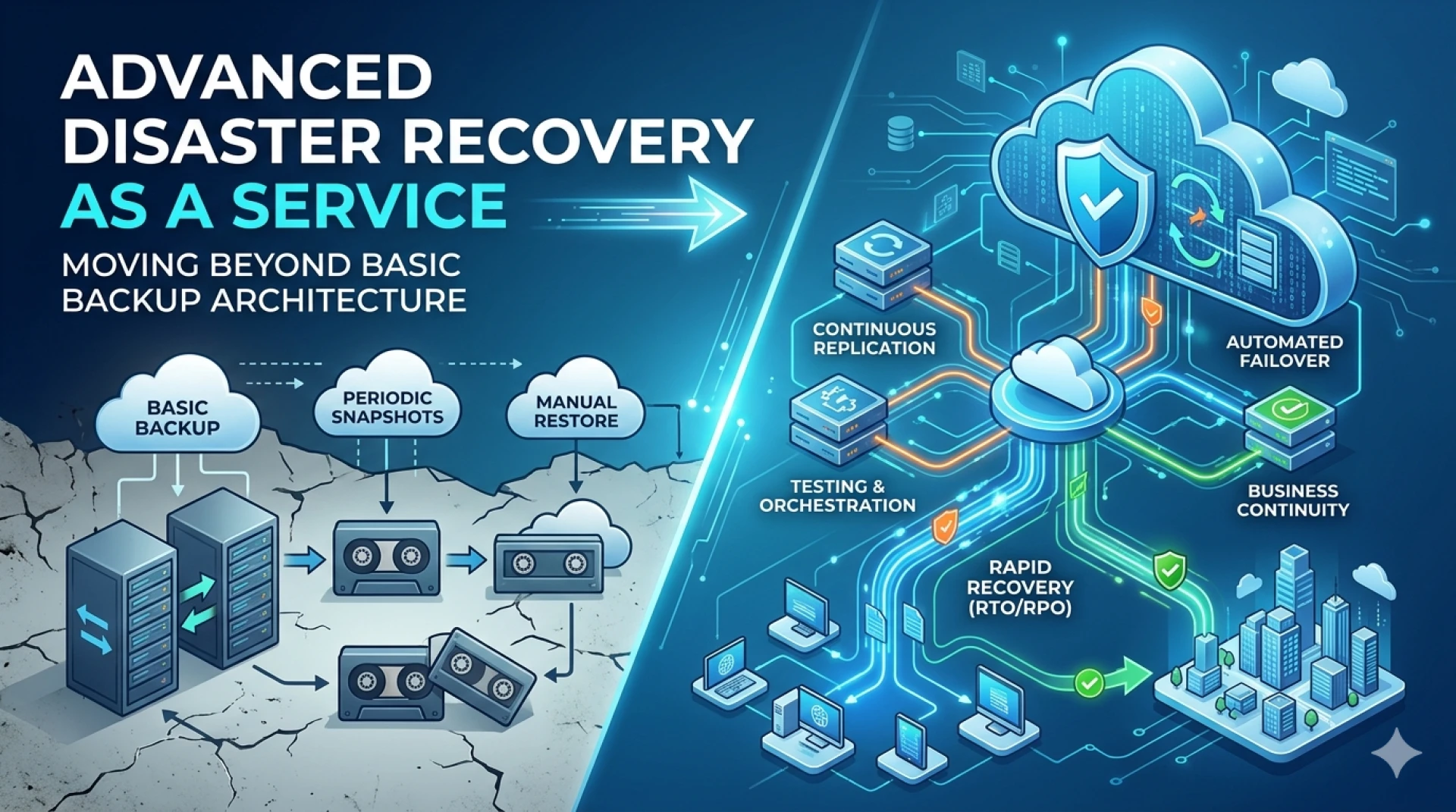
Disaster Recovery and Business Continuity
National security agencies require robust disaster recovery capabilities to maintain operations during natural disasters, cyberattacks, or other disruptive events. SAN storage enables synchronous and asynchronous replication to geographically distributed sites, ensuring that critical data remains available even during site-wide outages.
Snapshot technologies provide point-in-time recovery capabilities that enable rapid restoration of data to known-good states. This capability proves essential when responding to cyber incidents or data corruption events that might compromise operational systems.
Military Operations Support
Field operations require reliable access to intelligence data, maps, and operational information. SAN storage supports these requirements through high-performance computing clusters that can process and serve data to deployed systems in real-time.
Edge deployment capabilities extend SAN functionality to forward operating locations while maintaining secure connectivity to centralized data repositories. This distributed architecture ensures that field personnel have access to current intelligence while maintaining security protocols.
Security Considerations for National Security SAN Deployments
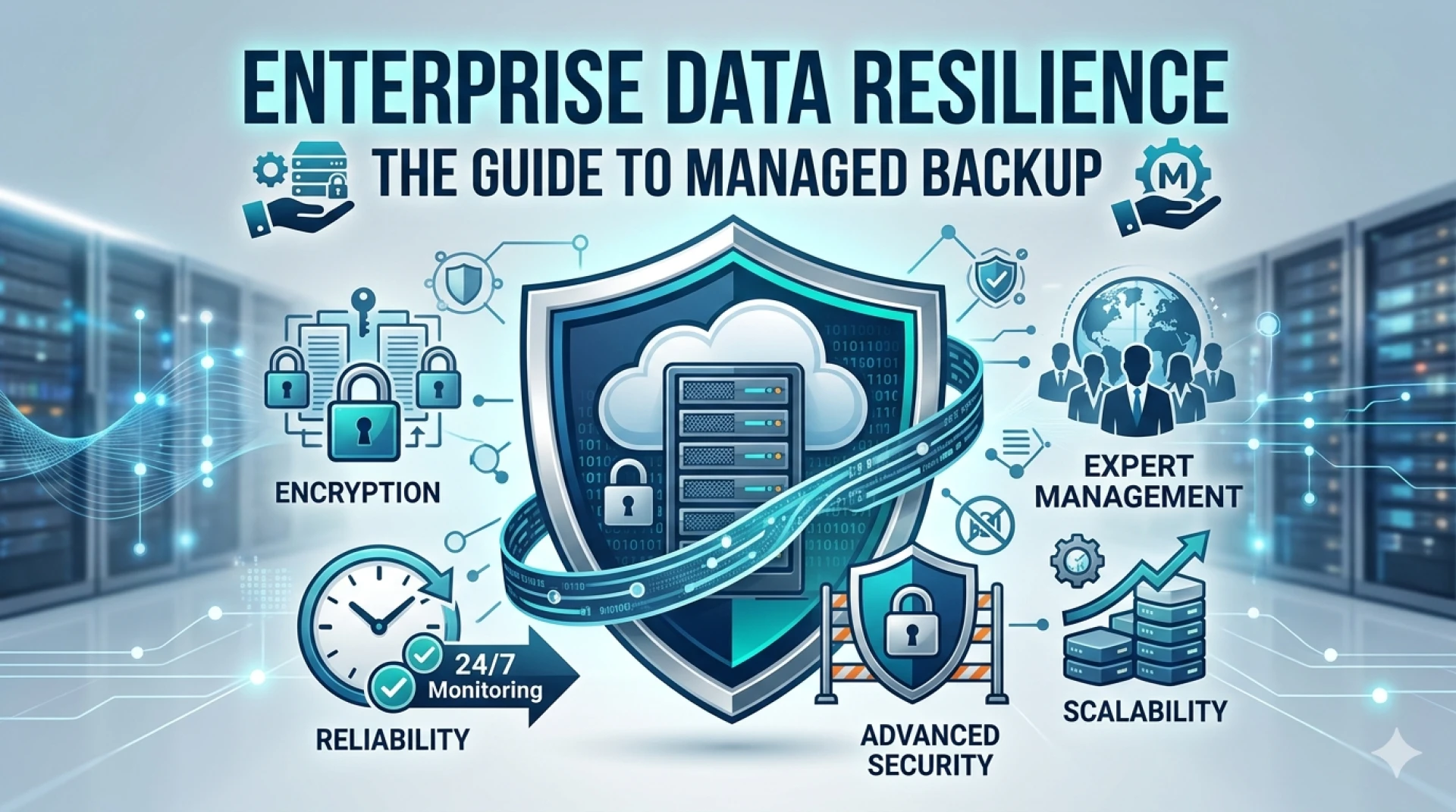
Encryption and Key Management
End-to-end encryption protects data throughout its lifecycle within SAN environments. Hardware security modules (HSMs) provide tamper-resistant key storage and cryptographic processing capabilities that meet federal standards for classified data protection.
Key management systems integrate with existing security infrastructure to provide centralized control over encryption keys while maintaining separation of duties required by security policies. Automated key rotation ensures that encryption keys remain current without impacting operational systems.
Access Control and Authentication
Role-based access control (RBAC) systems integrate with existing directory services to provide granular control over storage resources. Multi-factor authentication requirements ensure that only authorized personnel can access sensitive data repositories.
Privileged access management solutions monitor and control administrative activities within SAN environments. These systems provide detailed audit trails of all administrative actions while preventing unauthorized modifications to security configurations.
Auditing and Compliance Monitoring
Comprehensive logging capabilities capture all access attempts, configuration changes, and data movement activities within SAN environments. These audit trails provide the documentation necessary to demonstrate compliance with federal regulations and security standards.
Real-time monitoring systems alert security teams to suspicious activities or policy violations. Automated response capabilities can isolate compromised systems or restrict access based on predefined security policies.
Regulatory Compliance Framework
SAN storage platforms support compliance with federal regulations including FISMA, NIST cybersecurity frameworks, and DoD security requirements. Built-in compliance reporting tools generate the documentation necessary for security assessments and audits.
Configuration management systems ensure that SAN environments maintain approved security configurations throughout their operational lifecycle. Automated compliance checking identifies and remedies configuration drift that might introduce security vulnerabilities.
Future Trends in National Security SAN Storage
AI and Machine Learning Integration
Artificial intelligence capabilities are being integrated into SAN storage platforms to provide predictive analytics and automated threat detection. These systems can identify unusual data access patterns that might indicate insider threats or compromised accounts.
Machine learning algorithms optimize storage performance by predicting data access patterns and pre-positioning frequently accessed data on high-performance storage tiers. This capability improves response times for critical intelligence applications while reducing infrastructure costs.
Hybrid and Multi-Cloud SAN Deployments
Government cloud initiatives are driving the development of hybrid SAN architectures that extend on-premises storage to authorized cloud environments. These deployments maintain security controls while providing the scalability and flexibility that cloud resources offer.
Multi-cloud strategies provide resilience against single-provider failures while enabling agencies to leverage specialized cloud services for specific operational requirements. SAN technology provides the consistent data services necessary to support these distributed architectures.
Advanced Data Security Technologies
Quantum-safe encryption algorithms are being integrated into SAN platforms to protect against future quantum computing threats. These implementations ensure that current data investments remain secure as quantum technologies mature.
Zero-trust security models are being applied to SAN environments to provide continuous verification of access requests and data operations. This approach reduces the risk of insider threats and limits the impact of compromised credentials.
Strengthening National Defense Through Advanced SAN Infrastructure
SAN storage technology provides the foundation that enables national security and defense agencies to manage their most critical data assets effectively. The combination of high performance, robust security, and enterprise-scale reliability makes SAN the preferred storage architecture for classified data environments and mission-critical applications.
The evolving threat landscape requires storage infrastructure that can adapt to new security challenges while maintaining the availability and performance that national security operations demand. Modern SAN platforms deliver these capabilities through advanced features designed specifically for high-security environments.
Organizations evaluating SAN storage for national security applications should prioritize platforms that provide comprehensive security controls, proven reliability, and the scalability needed to support growing data requirements. The investment in robust SAN storage solution infrastructure pays dividends through improved operational efficiency, enhanced security posture, and the confidence that critical data assets remain protected and available when needed most.






Sign in to leave a comment.